Tor Browser Download
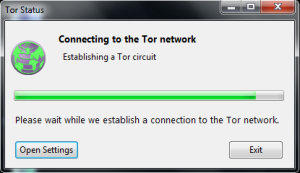
Tor Browser works by routing your internet connections through a network of volunteer servers making it difficult for others to track your location or monitor your activities.
Software details
Software Description
Tor Browser plays a role, in safeguarding privacy. Initially developed by the U.S. Naval Research Laboratory in the 2000s to secure government communications it is now overseen by the Tor Project. Their main focus is on improving privacy and security tools for users
The browser operates based on the onion routing principle encrypting internet traffic through layers and routing it through servers to conceal user location and browsing activity. This effectively enhances privacy and security.
Users can browse the internet anonymously with Tor Browser thanks to its routing of connections through volunteer run servers that hide user information from network surveillance. This makes it an essential tool for maintaining anonymity.
The browser caters to a audience, including journalists, activists and everyday individuals who use it for various purposes such as secure communication or bypassing internet restrictions. Its ability to protect user privacy makes it highly valuable in contexts.
For accessibility convenience Tor Browser is compatible with platforms, like Windows, macOS, Linux and Android devices.
This broad support, across platforms ensures that a wide range of people can make use of its functions. The Tor Project also offers guidance to assist users in navigating its usage.
Nevertheless the Tor Browser encounters obstacles and critiques. Some argue that it enables activities on the web. Law enforcement agencies have expressed concerns about its potential for misuse. Nonetheless the Tor Project advocates for the importance of privacy and freedom. They assert that the advantages of Tor in safeguarding rights and privacy outweigh any downsides.
Periodically the Tor Project issues updates for the browser. These updates address security weaknesses. Enhance privacy features. The project team works diligently to stay of security threats. Each update often includes solutions for known issues enhancing the security of the browser.
Lastly educational institutions and privacy advocates endorse the Tor Browser as a tool for educating people about internet privacy. A global network of volunteers supports the development and upkeep of the browser. This collaborative effort ensures its growth and relevance, in promoting privacy.